Revision history [back]
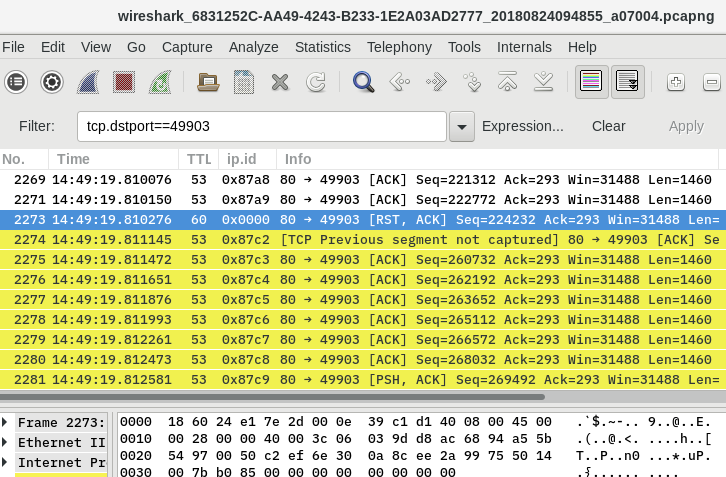
Your theory seems to be correct, the data segments arrive with a TTL of 53 and incrementing ip.id values.
The RST packet arrives with a TTL of 60 and an ip.id of 0.
After the reset there are still 8 full-sized segments arriving, however there is a gap of 24 segments.
So the session was terminated in the middle of a download by a device presumably being 4 hops away whereas the linux server is 11 hops away .
A tracert rentmaster.net will probably show that it's the device at the edge into the NTT network.
net-165-91-128-1.net.tamu.edu --> tamu-dlls-com.tx-bb.net
That still doesn't explain why this happens though.
It wouldn't surprise me if the session was dropped due to security / AV scanning
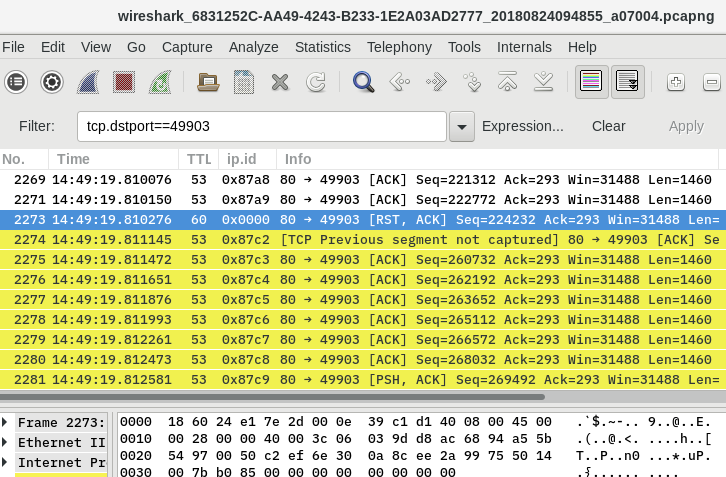
Your theory seems to be correct, the data segments arrive with a TTL of 53 and incrementing ip.id values.
The RST packet arrives with a TTL of 60 and an ip.id of 0.
After the reset there are still 8 full-sized segments arriving, however there is a gap of 24 segments.
So the session was terminated in the middle of a download by a device presumably being 4 hops away whereas the linux server is 11 hops away .
A tracert rentmaster.net will probably show that it's the device at the edge into to the NTT network.
net-165-91-128-1.net.tamu.edu --> tamu-dlls-com.tx-bb.net
It wouldn't surprise me if the session was dropped due to security / AV scanning